Turvallisten verkkojen puolesta
Siinä missä ennen etsittiin luonnon raaka-aineita kuumeisesti ja jopa likaisia temppuja hyödyntäen, on tulevaisuuden kenties kallein raaka-aine raaka data. Lähes koko maailma on verkottoitunut. Informaatioväylien kautta yksityiset ihmiset hoitavat elämänsä asiat aina syntymästä kuolemaan ja yritykset sekä valtiot luottavat suuresti verkkojen toimintaan. Mutta, kuten sanotaan, tieto on valtaa ja uudellakin aikakaudella on niitä, jotka hamuavat sitä keinolla millä hyvänsä.
Suomen tietoverkot kuuluvat eri tutkimusten mukaan puhtaimpiin maailmassa, mutta se ei tarkoita että voisimme tuudittautua turvallisuuden tunteeseemme. Rikolliset ja jopa valtiolliset toimijat etsivät jatkuvasti uusia aukkoja tietoverkkojen ja ohjelmistojen tietoturvasta. Heidän tavoitteenaan on yleensä rahallinen hyöty. Viime aikoina julkisuuteen on noussut puheenaiheeksi myös ns. hybridisodankäynti, jonka avulla vieraan vallan edustajat tai heitä kannattavat toimijat pyrkivät vaikuttamaan toisen maan toimintaan. Räikeimpiä esimerkkejä tällaisesta toiminnasta ovat valeuutissivustot, joilla on selvä poliittinen agenda sekä Yhdysvalloissa vellova tutkinta Venäjän tai venäjämielisten toimijoiden sekaantumisesta maan presidentinvaaleihin.
Näiden mediaseksikkäiden tapausten lisäksi tietoturvakysymykset ja -uhat ulottuvat myös tavallisten ihmisten arkeen. Monet muistavat törmänneensä ”nigerialais kirjeisiin”, jotka levisivät vuosituhannen alussa sähköpostitse. Loputkin ovat varmasti kuulleet ”phishing” -ohjelmistoista, joilla pyritään urkkimaan pankki- ja henkilötietoja erilaisten haittaohjelmien ja taktiikoiden avulla. Myös yritykset pohtivat jatkuvasti tietoturvaan liittyviä kysymyksiä, ja hyvästä syystä. Kuvitellaanpa hetki, miten vakava kriisi syntyisi, jos esimerkiksi suomalaiset pankit joutuisivat koordinoidun ja tehokkaan verkkohyökkäyksen kohteeksi. Maksuliikenne katkeaisi, tiedonvaihto pysähtyisi ja asiakastiedotkin voisivat päätyä joko julkiseen jakoon tai myyntiin Internetin pimeälle puolelle eli Dark Webiin.
Jotteivät rikolliset ja muut haittaa tavoittelevat toimijat pääsisi häiritsemään tietoverkkoliikennettä tai aiheuttamaan tuhoa, on Jyväskylän ammattikorkeakouluun perustettu jo vuonna 2011 uhkavektoreiden tunnistamiseen ja niiltä puolustautumiseen tähtäävä JYVSECTEC. Kyberturvallisuuteen erikoistunut JYVSECTEC sai vuonna 2011 rahoitusta Suomen johtavan kyberturvallisuuden tutkimus-, kehitys- ja koulutuskeskuksen kehittämiseen.

Hankepäällikkö Tero Kokkonen kertoo videolla, että hankkeissa on tehty kyberturvallisuusharjoituksia ja RGCE-niminen harjoitusympäristö. Yhteistyökumppaneita ovat Elisa, Telia, Cygate, Fingrid ja Airbus Defence and Space. Hankkeen päätyttyä jatketaan alan tutkimus- ja koulutustoimintaa. Jyväskylä on Kokkosen mukaan kyberkaupunki kyberturvallisuuteen liittyvän aktiivisen toiminnan ansiosta. Kansallisia kyberturvallisuusharjoituksia on järjestetty vuodesta 2013 alkaen.
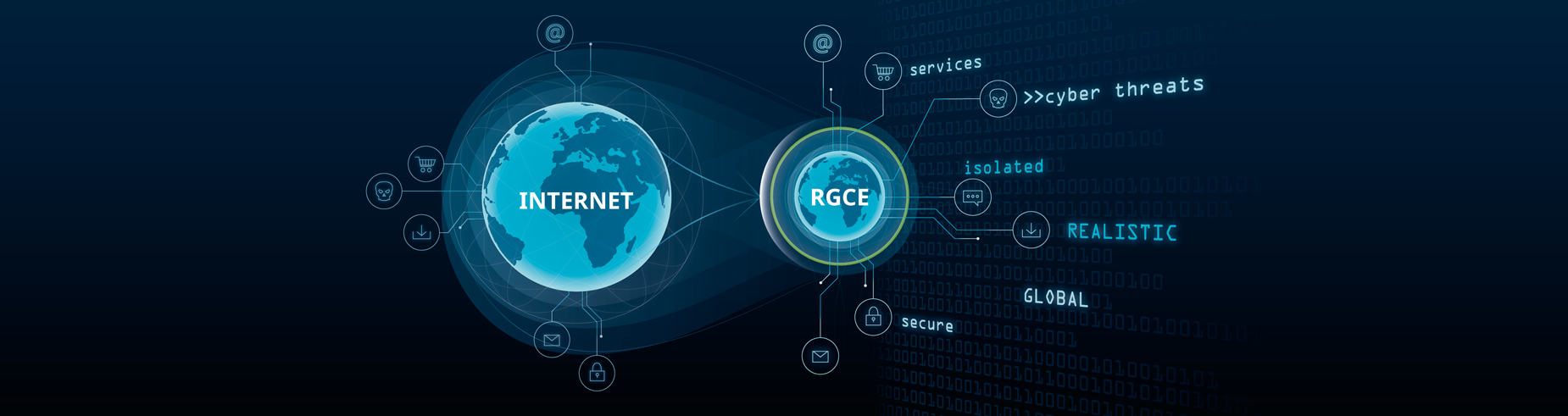
JYVSECTEC Center ja JYVSECTEC Center RGCE (Realistic Global Cyber Environment) hankkeilla pyritään lisäämään JYVSECTEC:in toimintaedellytyksiä sekä parantamaan sen toimintaa yritysten ja valtiollisten toimijoiden suuntaan. Hankkeiden avulla on rakennettu muun muassa ”tilannehuone”, jota yritykset ja muut toimijat voivat hyödyntää kyberturvallisuusharjoitusten käytössä. JYVSECTEC:in toiminta on laajasti noteerattu sekä yrityksissä että puolustusministeriössä ja puolustusvoimissa. Esimerkiksi puolustusministeriön turvallisuuskomitea mainitsi JYCSECTEC:in toiminnalla olleen merkittäviä vaikutuksia kyberturvallisuusstrategian toimeenpano-ohjelman kannalta. RGCE on tunnustettu kansainvälisellä tasolla Suomen laajimmilla ominaisuuksilla varustetuksi Cyber Range-toimintaympäristöksi, joten sillä on todella hyvät valmiudet kyberturvallisuuden parantamiseen.
Globaalissa mittakaavassa, Jyväskylän RGCE on yksi harvoista riippumattomista, ei-sotilaallisista Cyber Range toimintaympäristöistä. Riippumattomuuden lisäksi RGCE:n toiminta on poikkeuksellisen laajaa verrattuna muihin vastaaviin toimintaympäristöihin. Suomen laajimpana Cyber Range toimintaympäristönä, JYVSECTEC:in toiminta, johon kuuluvat opetuksen lisäksi myös yritysyhteistyö ja osallistuminen Suomen kansallisiin kyberharjoituksiin yhdessä puolustusvoimien kanssa, voi kehittyä vieläkin uraauurtavammaksi, sanoo Jyväskylän ammattikorkeakoulun IT-instituutin johtaja Mika Karjalainen.
”Uusia haittaohjelmia tulee koko ajan ja suurin haaste onkin pitää itsensä kehityksen aallonharjalla. Tätä varten meidän täytyy pitää kiinni osaajistamme.” -Mika Karjalainen
JYVSECTEC pyrkii soveltamaan akateemista ja yritysten tuottamaa tietoa kehittämässään RGCE -kybertoimintaympäristössä. Komealta kalskahtavan termin alle kätkeytyy vähintäänkin yhtä komea toiminta: RGCE on Internetiä simuloiva keinotekoinen ympäristö, jossa data kulkee samalla tavalla kuin ”oikeassa” Internetissä. Erona on vain verkkoliikenteen määrä, joka on RGCE:ssä skaalattu, kertoo JAMK:in IT-insitituutin lehtori ja hankepäällikkö Tero Kokkonen.
”RGCE:ssä voimme simuloida käyttäjäliikennettä, esimerkiksi sähköpostien kulkemista, Web-selailua ja videopalveluiden käyttöä. Tämä lisää realistisuutta, kun testaamme ja tutkimme erilaisia uhkavektoreita. Realistisuus tarkoittaa myös sitä, että voimme luoda helposti yhteistyökumppaniemme tai asiakkaidemme haluaman ympäristön”, Kokkonen paljastaa.

Jyväskylän ammattikorkeakoulun IT-instituutti tekee yhteistyötä Jyväskylän yliopiston sekä valtakunnan muiden yliopistojen ja korkeakoulujen kanssa, mikä on Suomen kokoisessa maassa äärimmäisen tärkeää, Kokkonen painottaa.
”Yhteistyömme yliopistojen kanssa hyödyttää molempia, sillä jo lähtökohtaisesti meillä on eriytetyt tavoitteet. Siinä missä yliopistot keskittyvät akateemiseen perustutkimukseen, ammattikorkeakoulujen toiminta on enemmän soveltavaa tutkimus- ja kehitystoimintaa. Tässä yhteydessä pystymme hyödyntämään RGCE:tä tutkimus- ja kehitysyhteistyössä toisten tutkimuslaitosten kanssa”, Karjalainen luonnehtii.
Sotaa bittiavaruudessa
JYVSECTEC:in RGCE-toimintaympäristössä on kokeiltu yritysyhteistyön lisäksi myös yhteiskunnan kriittisten toimijoiden valmiuksia vastata kyberuhkiin ja torjua niitä. Muun muassa jo vuonna 2016 RGCE oli keskeisessä roolissa, kun kansallinen kyberharjoitus järjestettiin valtionvarainministeriön ja puolustusvoimien johtamisjärjestelmäkeskuksen kanssa. Harjoituksilla simuloidaan erilaisia hyökkäys-, puolustus- ja kriisiskenaarioita. JYVSECTEC osallistui myös vuoden 2017 vastaavaan KYHA-harjoitukseen.
”Tarkoituksena RGCE:n toiminnassa on suorittaa tieturvatestauksia asiakkaille ja yhteistyökumppaneille. Testausten avulla etsitään tietoverkoista ja palveluista heikkouksia, joita rikolliset ja muut toimijat voisivat hyödyntää todellisessa verkkoympäristössä”, Karjalainen kuvaa.
Turvallinen kybertoimintaympäristö helpottaa yksilöiden ja yritysten oman toiminnan suunnittelua, mikä lisää taloudellista aktiviteettia. Hyvä toimintaympäristö parantaa myös Suomen kansainvälistä houkuttelevuutta investointikohteena. Näiden lisäksi kyberturvallisuus on itsessään uusi ja vahvistuva liiketoiminnan alue. Kansallinen kyberturvallisuus ja suomalaisten yritysten menestys ovat yhteydessä keskenään. -Suomen Kyberturvallisuusstrategia
Kyberharjoitukset liittyvät tiiviisti kansalliseen kyberturvallisuusstrategiaan, jota myös JYVSECTEC:issä seurataan tiiviisti.
”On hyvä, että on olemassa tavoitetila ja että eri toimijat ja päämäärät on tunnistettu kansallisella tasolla. Strategiassa on korostettu turvallisuustoimijoiden yhteistyötä ja strategia tunnistaa suomalaisen yhteiskunnan erityispiirteet”, Karjalainen miettii.

Kyberturvallisuus, sen työkalujen käyttö sekä tutkiminen ovat olleet myös tärkeässä roolissa Jyväskylän ammattikorkeakoulussa. Opiskelijat ovat voineet suorittaa ylemmän ammattikorkeakoulututkinnon cyber security -tutkinto-ohjelmasta vuodesta 2013 alkaen ensimmäisenä Suomessa. JAMK:in hattuun lyötiin yksi sulka lisää, kun se vuoden 2016 kesällä oli perustamassa European Cyber Security Organization (ECSO) -järjestöä.
Kyberturvallisuus on kenties tavalliselle kansalaiselle piilossa, niin kauan kuin se toimii, mutta kun jokin sen osa pettää, voivat ongelmat tulla voimakkaasti näkyviin myös arjessa. Viime keväänä poikkeuksellisen laaja ns. WannaCry-kyberhyökkäys iski Windows-käyttöjärjestelmiä käyttäviin koneisiin lukitsemalla ne ja vaatimalla käyttäjiltä lunnaita koneiden vapauttamista vastaan. Kenties näkyvin kyberhyökkäyksen uhri kyseisessä hyökkäyksessä oli Ison-Britannian julkinen terveydenhuoltojärjestelmä NHS, jonka toiminnan häiriintyminen johti vakaviin vaaratilanteisiin potilaiden hoidossa.
Suurin yksittäinen syy siihen, miksi WannaCry kyberhyökkäys oli niin laaja oli se etteivät käyttäjät olleet päivittäneet käyttöjärjestelmiään. Tämä oli myös syynä siihen, miksei hyökkäys aiheuttanut Suomessa saman mittakaavan tuhoja.

”Suomalaisilla teleoperaattoreilla ja käyttäjillä on korkea teknologinen osaaminen. Lisäksi Suomessa vallalla oleva mentaliteetti, eli se että sääntöjä noudatetaan ja tässä tapauksessa päivitetään järjestelmiä nopeasti ja usein, auttoi myös osaltaan tämän kyberhyökkäyksen torjumisessa. Kulttuurit, joissa ohjelmistoja ei päivitetä niin paljon, saivat osakseen suurimman osan hyökkäyksen aiheuttamista vahingoista”, Karjalainen kuvailee.
Suurimmat uhat kyberturvallisuuden saralla tulevat Karjalaisen mukaan rikollisesti toiminnasta, jossa raha ja valta ovat suurimmat motiivit. Digitalisaation ja tietoverkkojen kehittymisen seurauksena koko digitaalinen maailma on ihmisten hyppysissä, eivätkä rikolliset ole tässä asiassa poikkeus. Tavallisiin ihmisiin ja yrityksiin kohdistuvat uhat ovat erilaisia, sillä yrityksiin kohdistuu myös vakoilua, joka ei ole suurin huolenaihe yksityisillä henkilöillä.
Alueellista ja kansainvälistä osaamista
JYVSECTEC:in ydintoimia ovat kyberturvallisuusharjoitusten järjestäminen sekä opetus- ja koulutustoiminta. Näistä kenties näkyvintä on harjoitustoiminta, jossa mukana on ollut suuri määrä eri yrityksiä, muun muassa S-ryhmä ja Telia, Kokkonen kuvailee.
Osa yritysasiakkaista ei halua tulla Karjalaisen mukaan julkisuuteen. Silloin yritys toimisi ”honeypottina” rikollisille, jolloin he voisivat kokeilla hyökätä niiden kimppuun ikään kuin testatakseen puolustuksia ja osoittaakseen taitonsa. Toisille yrityksille taasen harjoitustoimintaan ja turvallisuustesteihin osallistuminen on brändivaltti, jonka avulla voidaan osoittaa yrityksen tietoverkkojen puhtaus ja luotettavuus.

Eräs jo hankekokonaisuuden ensimmäisessä vaiheessa mukana ollut yritys on Airbus DS Finland, jonka toimitusjohtaja Vesa Arkko kiittelee JYVSECTEC:in toimintaa. Erityisesti kiitosta saa työntekijöiden koulutus sekä verkostoituminen.
”Meille päähyöty yhteistyöstä JYVSECTEC:in kanssa on ollut testausmahdollisuudet ja erilaiset koulutustilaisuudet”, Arkko jatkaa.
Myös hänen mukaansa rikollinen kybertoiminta on kasvanut merkittävästi, mikä toisaalta tarjoaa tietoturvan parissa toimiville yrityksille uusia liiketoimintamahdollisuuksia. Arkon mukaan Suomessakin tarvittaisiin isompaa panostusta kyberturvallisuuteen. Sitä ei kuitenkaan välttmättä ole näkyvissä, ilman suuren luokan kriisiä, jonka mukana ihmisten ymmärrys kyberturvallisuuden tärkeydestä nousisi.
Toiminnan kautta myös JYVSECTEC:in omat asiantuntijat oppivat uutta sekä pystyvät pitämään tietotaitonsa veitsenterävänä, mikä on kyberturvallisuuden alalla elintärkeää. JYVSECTEC ja IT-instituutti kouluttavat opiskelijoista IT-alan huippuluokan osaajia sekä kasvattavat opetus- ja tutkimushenkilökunnan tietotaitoa jatkuvasti, Karjalainen valaisee.
”Hankkeiden kautta saamme tuotettua alueellisesti osaamista ja työpaikkoja, jotka mahdollistavat myös tulevaisuuden toiminnan alueella”, hän jatkaa.

JYVSECTEC:iin tiiviisti liittyvä hanke on Finnish Cyber Security Certificate (FINCSC), joka on suunnattu erityisesti PK-yrityksille. Hankkeen tavoitteena on luoda riittävän yhdenmukaistettu kyberresilienssi-testi ja arviointityökalu, jonka läpäistyään yritys saa tunnustetun sertifikaatin. Sertifikaatti toimii takeena siitä, että yrityksen kyberturvallisuus on hyvällä tasolla ja sen toiminta on luotettavaa.
”Kansalaisina olemme äärimmäisen riippuvaisia PK-yrityksistä”, Kokkonen painottaa, ”ja juuri siksi niiden kyberturvallisuuteen keskittyminen on tärkeää”.